Analysis Exercise
by Coleman Kane
The demonstration that we’ll be doing today will walk through a number of files that I generated by running the following utilities on my compromised Win7 VM, after performing some actions through the Pupy RAT shell.
- winpmem & Volatility
- Mft2Csv
- Autoruns
- regedit.exe - part of Windows
- netstat.exe - part of Windows
Video Discussion:
Video analysis/investigation:
These analyze the following aspects of the system, to assist the analyst in gleaning information about how the malware behaves on the system, and what it did:
- System memory / running programs
- Filesystem directory
- Windows configuration specific to automatic execution (
autoruns) - Other windows configuration changes that might be helpful to look for
- Internet Explorer browser history
An archive containing many useful tools, including those discussed today, is available here:
System memory analysis
Using winpmem on the Windows VM, system memory was captured using the following command, and the resulting *.aff4 file was copied into the Kali VM:
winpmem-2.1.post4.exe --output <filename>.aff4 --format raw
Next, the PhysicalMemory artifact was extracted from the *.aff4 archive using unzip in Kali:
mkdir -p memdump
unzip filename.aff4 PhysicalMemory -d memdump/
I have created a file named vol_mods.txt which contains a list of volatility
modules that are somewhat quick to run and yield some decent output. I downloaded the above-linked file into the Kali image, and I ran the following
script from inside the memdump folder, created above:
(while read r
do volatility -f PhysicalMemory --profile=Win7SP1x86_23418 "${r}" --output-file="${r}.txt"
done) < vol_mods.txt
The above will run a loop across each of the volatility modules and place the output for each into a textfile under memdump/ that is named
after the module.
There is a very useful timeliner.txt output that combines a lot of the data from other data sources into a timeline of activity. Included in
this, as well as in its own analysis file named iehistory.txt, is the Internet Explorer history - which is ingrained in Windows versions prior
to 10, as the web browser was a core component of the operating system.
I have generated some example data here:
Filesystem Directory
Using Mft2Csv.exe, I generated a timeline of filesystem activity that matches the format that a tool like log2timeline would output. However,
a nice feature of Mft2Csv.exe is that I can execute it from within the running system:
Mft2Csv.exe /Volume:c: /ExtractResident:1 /OutputPath:<outputfolder> /TimeZone:-5 /OutputFormat:l2t /ScanSlack:1
When running Mft2Csv, it will be important to keep in mind that it creates a new folder where you tell it to place all of its
output files, so you only need to provide a destination folder where you would like this to be created, such as Desktop or Documents
or even the network path of a shared folder you’ve configured in VirtualBox (\\VBOXSVR\sharedfolder\ ).
This will create a large *.csv file inside of a timestamped folder that will have all of the file timestamps tabled out, one per row,
so you will not only be able to navigate files, but also the timeline of their lifespan. These timestamps represent the 4 timestamps that
Windows NTFS keeps track of for each file, typically described as MACB or MAC(b):
- Modified
- Accessed
- Changed (directory entry / metadata modified)
- “Born” or “Created”
The following documentation from Andrea Fortuna discusses this convention and how Windows uses them, in detail:
Some files that we will go over from this:
Depending upon the size of the filesystem, the CSV file generated can get quite large. I recommend installing gnumeric. Under Kali, you can install this with the following command:
apt install -y gnumeric
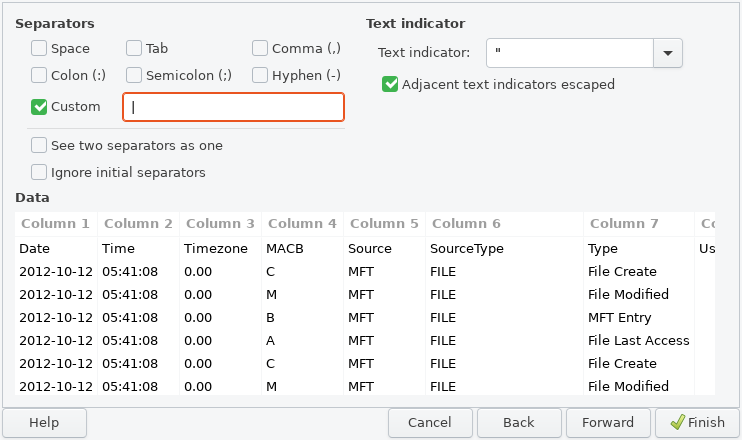
For gnumeric, don’t open the CSV directly. Instead, open the program as if you were creating a new spreadsheet,
and then from the File menu, choose Import Data, and then Import Text File… to import the data. It will take a
short while to parse through the whole data, but the dialog it presents will provide you with an option to separate
fields using the pipe (|) character.
Registry Data
I’ve used the core Windows utility regedit.exe to export a text version of the Windows registry. Some of the tools used in volatility as well
as autoruns will analyze data within the registry. We will look at the file format and discuss its contents, as well as review how the known persistence
data appears within it.
The dump of my registry data:
Autoruns
Key to malware is maintaining persistence on a system. This is basically the act of making sure that the installed backdoor maintains or continues to attempt to create a connection back to the command and control system, across users logging in and out, and across reboots and system moves (such as a laptop going from school, to work, to home, to Highland Coffee, etc.).
Microsoft released an OS inspection utility called autoruns that will analyze registry, installed special file locations, services, and some other aspects of the OS, to identify if anything is configured in well known locations for auto-loading on boot.
An output of this utility is provided here:
Network Connections
Additionally, surveying the system for active network connections can be done using the built-in netstat utility. A common approach is to
run it while disabling IP->name resolution (-n speeds up running), display all open and listening ports (-a), and associate each with
the application and PID that own them (-b).
netstat -a -n -b > netstat_anb.txt
A copy of the one I created is here:
Notes from Video
The notes I took during my analysis video are below:
Known Bad: 192.168.56.104
--------------------------
Program/Filename: invoice.exe
Times accessed: 04:12:22, 04:34:19 - 2020-01-28
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run -> C:\Windows\invoice.exe (6:24 AM 1/28)
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\invoice.exe (04:27:04 1/28 - opened)
%windir%\system32\invoice.exe (05:22:21 1/28 - opened)
shimcache.txt:2020-01-28 04:12:22 UTC+0000 \??\C:\Windows\invoice.exe
shimcache.txt:2019-02-22 06:03:06 UTC+0000 \??\C:\Windows\System32\invoice.exe
shimcache.txt:2019-02-22 06:03:06 UTC+0000 \??\C:\Users\IEUser\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\invoice.exe